- AppSheet
- AppSheet Forum
- AppSheet Q&A
- Preview As allows users to be added which are NOT ...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
In testing I added a user in the Preview As which was not in my White/Allow List or the User table of my app. The App allowed them to be added to my User table which should NOT happen if they are not on the White/Allow List.
Is this due to the inconsistencies we see with the Preview As, where it sometimes see the User behind the scene as the actual logged in to AppSheet user and NOT the Preview As?
I’m trying to see what happens when someone who is not on the White/Allow List tries to get into my app.
- Labels:
-
Errors
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
The allow list in the app editor controls who can sign-into the app and can be used to assign roles to signed-in users. This allow list has no effect whatsoever (to my knowledge and expectation) on the behavior of the app unless you design the app to use the information the allow list provides (via USEREMAIL() and USERROLE()). If the Preview As feature enforced the allow list, you’d have to give the user access before you could test the app against their user.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Just to be clear, when I add users via the add User Emails, as seen in screenshot …
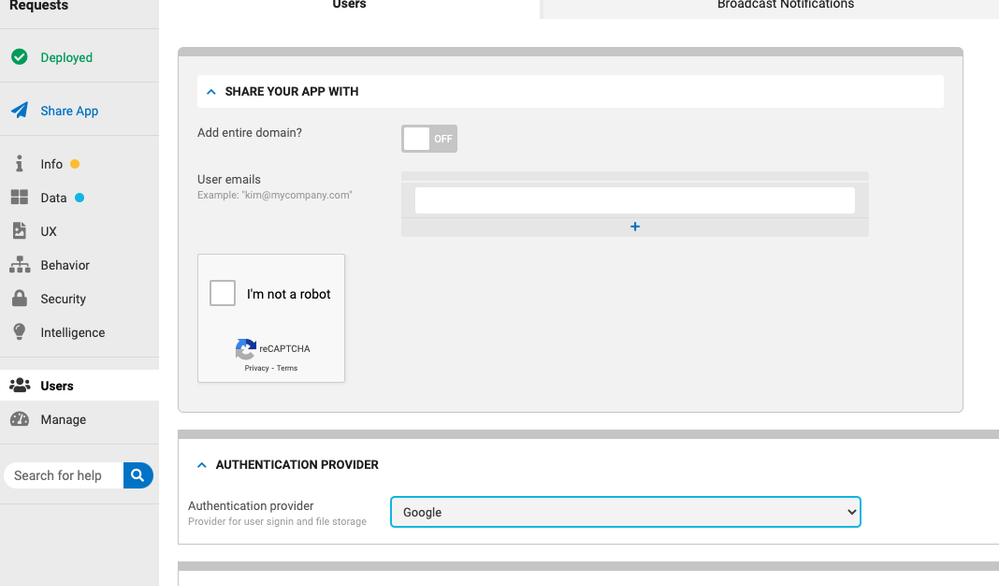
Only those users who have been added can actually log into my app? Correct?
Then, since I added a register page, they have to complete that to be added to my app. I use: IN(USEREMAIL(),USERS[USER_EMAIL]) to make sure a user that isn’t in my Users table can’t see anything but the registration form.
The Preview As doesn’t care if an email is in the Allow List? But then the App takes over and forces that unregistered user to go through the registration form.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
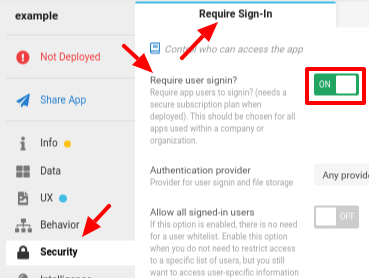
Your app must require sign-in:
In the image above, note also the Allow all signed in users option. If OFF (as shown), then only those users listed in the allow list may use your app.
That is a legitimate approach to hiding views, sure. It does not prevent a skilled user from accessing hidden views, though. Nor does it prevent data you don’t want the user to see from reaching the user’s device.
I do not believe Preview As considers the allow list at all.
If your app is designed to do that, yes.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Yes, I have Require User Sign In ON and Allow all signed in users OFF. Thanks for pointing those out. I knew I had them set but couldn’t remember where.
Steve, How can a skilled user that is NOT in my Allow List, access hidden views? I assume it is in the browser version?
That is a legitimate approach to hiding views, sure. It does not prevent a skilled user from accessing hidden views, though. Nor does it prevent data you don’t want the user to see from reaching the user’s device.
I am currently working on Security Filters to limit data downloaded.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
To clarify…
-
If your app requires sign-in, a user that is not signed-in cannot see anything in your app.
-
If your app requires sign-in and does not allow all signed-in users, a user that is not in your allow list cannot see anything in your app.
If a user is allowed into your app, that user can enter a URL into their browser to access you app. That URL can directly reference any view in your app, or even target specific tables and rows without regard to views. Doing so bypasses all navigation the app presents and sidesteps any Show if constraints placed on views.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
True, you can hack the hell out of it - but you have to know what to put in order for it to work. If your table names make sense, people will be able to suss them out eventually; then, like Steve said, someone could hack the URL and access a root table view and see all the records for that table.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks for the reassurance. I used the Incognito window tip to see how it really looks to a user not on my Allow List.
Thanks for the detailed explanation. That must be why you have stated multiple times that app info should be hidden on the URL.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Just thought I would chime in here @Lucinda_Mason.
That “Preview as” function inside the editor isn’t really a TRUE representation of what the experience will be like when using the app as that email.
Some things kinda get confused as to who you are; it sees the email you’ve entered, but it also sees the email you’ve used to log into the editor - and it doesn’t quite know how to handle it.
The best approach for testing your app as if from another perspective, is to actually go that route.
Thankfully, it’s super easy to create an incognito window and log into your app using the credentials you want. ![]()
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks for the tip. I’ve never used an incognito window so I’ll look into that.
Wow. Incognito is cool. Thanks for pointing me to it.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
You’re welcome.
The “Preview As” is really helpful, but sometimes it just get’s confused.
![]()
-
Account
1,676 -
App Management
3,098 -
AppSheet
1 -
Automation
10,320 -
Bug
982 -
Data
9,676 -
Errors
5,732 -
Expressions
11,777 -
General Miscellaneous
1 -
Google Cloud Deploy
1 -
image and text
1 -
Integrations
1,609 -
Intelligence
578 -
Introductions
85 -
Other
2,903 -
Photos
1 -
Resources
537 -
Security
827 -
Templates
1,308 -
Users
1,558 -
UX
9,109
- « Previous
- Next »
| User | Count |
|---|---|
| 39 | |
| 28 | |
| 24 | |
| 24 | |
| 13 |

 Twitter
Twitter